Decoding New Data Privacy Guidelines: What Businesses Need to Know for April 2026

The landscape of data protection is constantly evolving, and businesses across the United States are bracing for a significant overhaul. In a move poised to reshape how organizations collect, process, and store personal information, new federal data privacy guidelines are slated to roll out in April 2026. This comprehensive regulatory framework aims to standardize data protection practices, enhance consumer rights, and impose stricter obligations on businesses. For any entity handling personal data, understanding these forthcoming changes is not merely advisable but absolutely critical for sustained operation and avoiding severe penalties.
The impending April 2026 deadline might seem distant, but the complexities involved in achieving full compliance necessitate immediate attention and proactive planning. These guidelines represent a pivotal moment, signaling a shift towards a more unified and robust approach to data privacy at the federal level. Companies that begin their preparations early will be better positioned to adapt, mitigate risks, and even leverage these changes to build greater trust with their customer base.
This article delves deep into the specifics of the new federal data privacy guidelines, dissecting their core components, potential impact, and offering actionable strategies for businesses to navigate the path to compliance. From understanding consumer rights to implementing robust data governance frameworks, we will cover everything you need to know to be ready for April 2026.
The Genesis of New Federal Data Privacy Guidelines
For years, the United States has operated under a patchwork of sector-specific data privacy laws (like HIPAA for healthcare and GLBA for financial institutions) and a growing number of state-level regulations (such as CCPA/CPRA in California, VCDPA in Virginia, and CPA in Colorado). While these laws have provided some level of protection, the lack of a comprehensive federal standard has led to fragmentation, legal complexities for businesses operating across state lines, and inconsistencies in consumer rights.
The push for new federal data privacy guidelines stems from several factors:
- Increasing Data Breaches: The frequency and scale of data breaches have highlighted the urgent need for stronger security measures and accountability.
- Global Standards: The success and influence of regulations like the European Union’s General Data Protection Regulation (GDPR) have demonstrated the effectiveness of comprehensive privacy frameworks.
- Consumer Demand: A growing public awareness and demand for greater control over personal data have put pressure on lawmakers to act.
- Technological Advancements: The rapid evolution of technologies like AI, big data analytics, and IoT has introduced new challenges and ethical considerations regarding data use.
These new guidelines are designed to address these challenges head-on, providing a unified approach that aims to simplify compliance for businesses while empowering consumers with enhanced rights. The April 2026 deadline is a clear signal that this is not a suggestion, but a mandatory evolution in data management practices.
Key Pillars of the New Federal Data Privacy Framework
While the full text of the guidelines is extensive, several core principles and requirements are expected to form the bedrock of the new federal data privacy framework. Businesses should familiarize themselves with these foundational elements:
1. Expanded Consumer Rights
At the heart of the new regulations is the empowerment of individuals regarding their personal data. Expect rights similar to those found in GDPR and CCPA, including:
- Right to Know: Consumers will have the right to know what personal data is being collected about them, the purpose of its collection, and with whom it is shared.
- Right to Access: Individuals can request access to their personal data held by an organization.
- Right to Correction/Rectification: Consumers can request that inaccurate or incomplete personal data be corrected.
- Right to Deletion/Erasure: The right to request the deletion of personal data, with certain exceptions.
- Right to Opt-Out: The ability to opt-out of the sale or sharing of their personal data for targeted advertising purposes.
- Right to Data Portability: The right to receive their personal data in a structured, commonly used, and machine-readable format, and to transmit that data to another controller.
Implementing mechanisms to easily facilitate these requests will be a significant undertaking for many businesses. This includes establishing clear procedures, designated points of contact, and robust internal systems to handle and respond to consumer requests within specified timeframes.
2. Data Minimization and Purpose Limitation
The new guidelines will likely emphasize principles of data minimization and purpose limitation. This means:
- Data Minimization: Businesses should only collect personal data that is absolutely necessary for a specified, explicit, and legitimate purpose. Avoid collecting data ‘just in case’ it might be useful later.
- Purpose Limitation: Personal data should only be processed for the purposes for which it was collected. Any new processing activity requires a new legitimate basis and, often, renewed consent.
This principle requires a thorough review of current data collection practices and a critical assessment of whether all data being gathered is truly essential for business operations. It encourages a ‘less is more’ approach to data, which can also reduce the risk exposure in case of a breach.
3. Enhanced Consent Requirements
Expect a stricter definition of consent. Implied consent or pre-checked boxes will likely be insufficient. The standard for consent is moving towards:
- Freely Given: Consent must be given without coercion.
- Specific: Consent must be given for specific purposes, not broad, undefined uses.
- Informed: Individuals must be fully aware of what they are consenting to, presented in clear, plain language.
- Unambiguous: Requires a clear affirmative action by the user (e.g., clicking a specific ‘I agree’ button, not just continuing to browse).
- Easily Withdrawn: Consumers must be able to withdraw consent as easily as they gave it.
This will necessitate a review of all consent mechanisms, particularly for marketing activities, website cookies, and data sharing with third parties. Privacy policies will need to be updated to be transparent and easily understandable.
4. Robust Data Security Measures
While data security has always been important, the new federal data privacy guidelines will likely mandate specific, robust security measures to protect personal data from unauthorized access, loss, or disclosure. This could include requirements for:
- Encryption: Mandatory encryption of sensitive data both in transit and at rest.
- Access Controls: Strict controls over who can access personal data, based on job role and necessity.
- Regular Audits and Assessments: Conducting routine security audits, penetration testing, and vulnerability assessments.
- Incident Response Plans: Developing and implementing comprehensive data breach response plans.
- Employee Training: Mandatory and regular training for all employees on data privacy best practices and security protocols.
The emphasis will be on implementing ‘appropriate technical and organizational measures’ to ensure a level of security commensurate with the risk. This is not a one-time fix but an ongoing commitment to data protection.
5. Data Protection Assessments (DPA/PIA)
For certain high-risk processing activities, businesses may be required to conduct Data Protection Assessments (DPAs) or Privacy Impact Assessments (PIAs). These assessments help identify and mitigate privacy risks before new systems or processes are implemented. This proactive approach ensures that privacy considerations are embedded into the design of products and services, rather than being an afterthought.
6. Vendor Management and Third-Party Data Sharing
The new guidelines will likely extend accountability to third-party vendors and service providers who process personal data on behalf of a business. Organizations will be responsible for ensuring that their partners also comply with the federal data privacy standards. This means:
- Due Diligence: Thorough vetting of all third-party vendors for their data protection practices.
- Contractual Obligations: Implementing robust data processing agreements (DPAs) that clearly define roles, responsibilities, and security requirements.
- Monitoring: Ongoing monitoring of vendor compliance.
This aspect will require a comprehensive review of all vendor contracts and a more stringent vendor selection process.
Preparing for April 2026: A Strategic Roadmap
The April 2026 deadline is approaching faster than it seems. Proactive preparation is key to ensuring compliance and minimizing disruption. Here’s a strategic roadmap for businesses:
Step 1: Conduct a Data Audit and Mapping Exercise
You can’t protect what you don’t know you have. The first critical step is to understand your data landscape. This involves:
- Identify all personal data: Catalog all types of personal data your organization collects, processes, stores, and shares.
- Data Flow Mapping: Document where this data comes from, where it goes, who has access to it, and where it is stored (both internally and with third parties).
- Purpose Identification: For each piece of data, clearly define the legitimate business purpose for its collection and processing.
- Retention Policies: Establish clear data retention schedules, ensuring data is not kept longer than necessary.
This exercise will reveal potential gaps, unnecessary data collection, and areas of high risk. It forms the foundation for all subsequent compliance efforts.
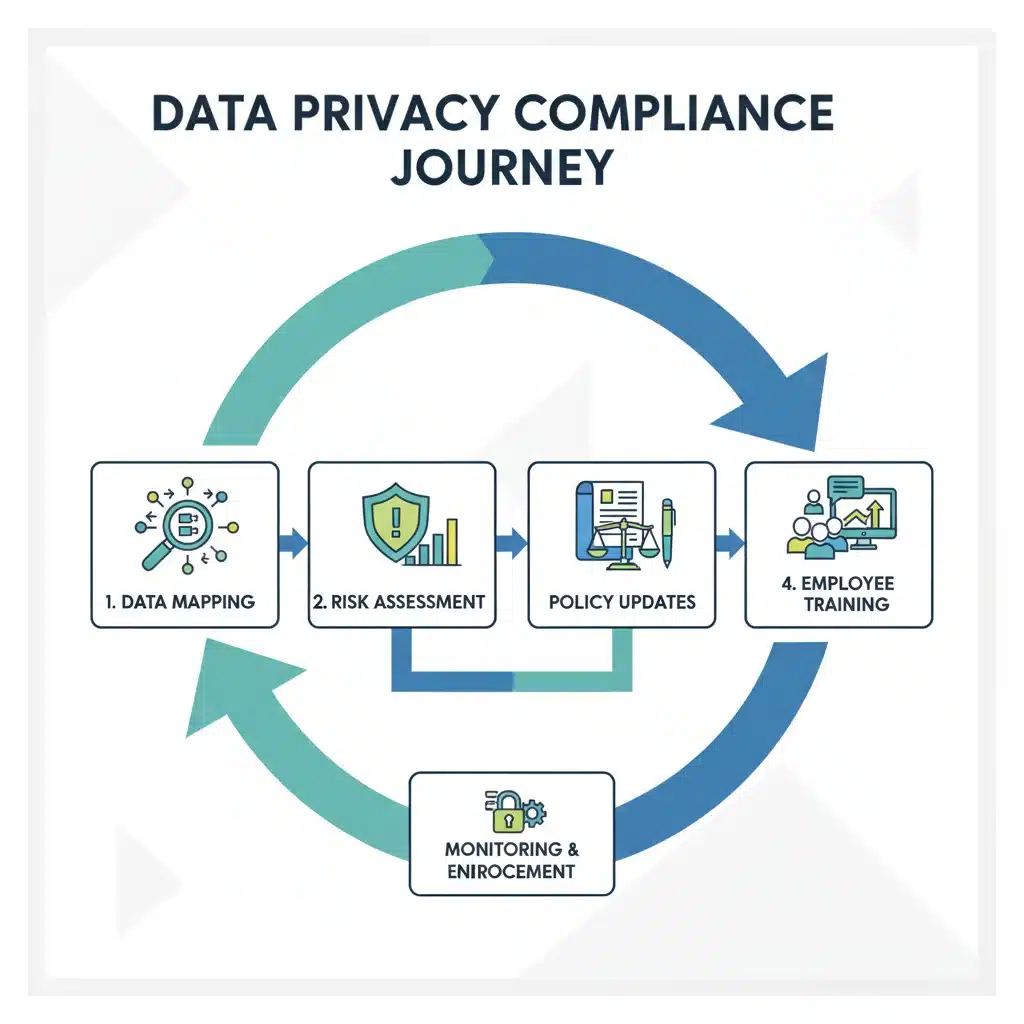
Step 2: Review and Update Privacy Policies and Notices
Transparency is paramount. Your privacy policies, website notices, and consent forms must be updated to clearly and concisely inform users about your data practices. Ensure they are:
- Comprehensive: Covering all aspects of data collection, use, sharing, and retention.
- Easy to Understand: Written in plain language, avoiding legal jargon.
- Accessible: Easily found on your website and applications.
- Reflective of New Rights: Clearly outlining consumer rights and how individuals can exercise them.
This is also an opportunity to re-evaluate your consent mechanisms to ensure they meet the stricter criteria of the new federal data privacy guidelines.
Step 3: Enhance Data Security Measures
Strengthening your cybersecurity posture is non-negotiable. This involves:
- Technical Safeguards: Implementing or upgrading encryption, multi-factor authentication, intrusion detection systems, and secure configurations.
- Organizational Safeguards: Reviewing and updating access control policies, data backup and recovery procedures, and incident response plans.
- Regular Testing: Conducting routine penetration testing and vulnerability assessments to identify and address weaknesses.
- Third-Party Security: Ensuring all third-party vendors and service providers adhere to your security standards and contractual obligations.
Consider engaging cybersecurity experts to perform a comprehensive security audit and recommend necessary improvements.
Step 4: Establish Data Subject Request (DSR) Procedures
With expanded consumer rights, your organization must be equipped to handle Data Subject Requests efficiently and effectively. This includes:
- Designated Contact Points: Clearly communicating how individuals can submit requests (e.g., dedicated email, web form).
- Verification Processes: Implementing robust methods to verify the identity of the requester to prevent unauthorized access.
- Internal Workflows: Establishing clear internal procedures for receiving, tracking, fulfilling, and documenting DSRs within the mandated timeframes.
- Automated Tools: Exploring privacy management software that can help automate aspects of DSR fulfillment and record-keeping.
Failure to respond adequately to DSRs can lead to significant penalties and reputational damage.
Step 5: Implement Employee Training and Awareness Programs
Your employees are your first line of defense in data privacy. Comprehensive and ongoing training is crucial:
- General Awareness: Educating all employees about the importance of data privacy, the new federal data privacy guidelines, and their role in protecting personal data.
- Role-Specific Training: Providing specialized training for employees who handle personal data regularly (e.g., HR, marketing, IT, customer service).
- Phishing and Social Engineering: Training on how to identify and report phishing attempts and other social engineering tactics.
- Policy Enforcement: Ensuring employees understand and adhere to internal data privacy policies and procedures.
Regular refreshers and updates to training content are essential to keep pace with evolving threats and regulatory changes.
Step 6: Appoint a Data Protection Officer (DPO) or Privacy Lead
Depending on the size and nature of your data processing activities, the new guidelines may mandate the appointment of a Data Protection Officer (DPO). Even if not strictly required, designating a privacy lead or a compliance team is highly recommended. This individual or team will be responsible for:
- Overseeing compliance efforts.
- Acting as a point of contact for regulatory authorities and data subjects.
- Conducting privacy impact assessments.
- Advising on data protection best practices.
This role is crucial for embedding a culture of privacy within the organization and ensuring ongoing adherence to the new federal data privacy standards.
Step 7: Develop an Incident Response Plan
Despite best efforts, data breaches can occur. A well-defined and regularly tested incident response plan is critical. This plan should:
- Detection: Outline procedures for promptly detecting security incidents.
- Containment: Steps to limit the damage and prevent further unauthorized access.
- Eradication: Measures to remove the cause of the incident.
- Recovery: Restoring systems and data to normal operation.
- Notification: Clear protocols for notifying affected individuals and regulatory authorities within mandated timeframes.
- Post-Incident Review: Analyzing the incident to prevent future occurrences.
Regular tabletop exercises and simulations can help refine your organization’s response capabilities.
The Broader Impact of Federal Data Privacy Guidelines
The introduction of comprehensive federal data privacy guidelines will have far-reaching implications beyond mere compliance:
Increased Consumer Trust
Companies that demonstrate a strong commitment to data privacy and transparency will likely build greater trust with their customers. In an era where data breaches are common, privacy-conscious consumers are more likely to choose businesses that prioritize their data protection.
Competitive Advantage
For many businesses, achieving compliance will be a challenge. Those that proactively embrace the new standards can gain a competitive edge by differentiating themselves as trustworthy data stewards. This can attract new customers and retain existing ones who value privacy.
Operational Efficiency and Data Governance
The process of preparing for these regulations forces companies to get a better handle on their data. Data mapping, minimization, and lifecycle management lead to improved data governance, reduced data clutter, and often, more efficient operations.
Reduced Legal and Reputational Risk
Non-compliance with the new federal data privacy guidelines can result in substantial fines, legal challenges, and severe reputational damage. Proactive compliance is an investment in risk mitigation, protecting both the financial health and public image of the organization.

Challenges and Considerations
While the benefits are clear, businesses will undoubtedly face challenges in adapting to the new federal data privacy framework:
- Resource Allocation: Compliance requires significant investment in time, personnel, technology, and legal expertise.
- Legacy Systems: Older IT infrastructures may not be designed with privacy by design principles, requiring substantial upgrades or overhauls.
- Complexity of Data Ecosystems: Modern businesses often interact with numerous data sources, cloud providers, and third-party services, making data mapping and control complex.
- Evolving Threat Landscape: Cybersecurity threats are constantly evolving, requiring continuous vigilance and adaptation of security measures.
- Maintaining Compliance: Compliance is not a one-time event but an ongoing process that requires continuous monitoring, auditing, and adaptation.
It will be crucial for businesses to view these challenges not as insurmountable obstacles but as opportunities for strategic improvement and long-term resilience.
The Role of Technology in Federal Data Privacy Compliance
Technology will play a pivotal role in helping organizations meet the new federal data privacy requirements. Several categories of tools and solutions can assist in this endeavor:
- Privacy Management Platforms: These platforms help automate data mapping, DSR fulfillment, consent management, and policy enforcement.
- Data Loss Prevention (DLP) Solutions: DLP tools monitor and control data in motion, in use, and at rest to prevent sensitive information from leaving the organization’s control.
- Identity and Access Management (IAM) Systems: IAM solutions ensure that only authorized individuals have access to specific data, enforcing granular access controls.
- Encryption Technologies: Robust encryption solutions are essential for protecting data both when it’s being transmitted and when it’s stored.
- Security Information and Event Management (SIEM) Systems: SIEM tools aggregate and analyze security events from various sources, providing real-time threat detection and incident response capabilities.
- Consent Management Platforms (CMPs): Specifically designed to manage user consent for cookies and other data processing activities, ensuring compliance with strict consent requirements.
Investing in the right technology can streamline compliance efforts, reduce manual errors, and provide an auditable trail of privacy activities.
Looking Ahead: The Future of Data Privacy
The new federal data privacy guidelines are not the end of the journey but a significant milestone in the ongoing evolution of data protection. As technology continues to advance and societal expectations around privacy shift, further refinements and new regulations are inevitable. Businesses should adopt a mindset of continuous improvement and adaptation when it comes to data privacy.
The move towards a unified federal standard in the U.S. will likely have a harmonizing effect, potentially simplifying the compliance landscape for businesses operating nationally, though careful attention will still be needed for specific state-level nuances that may remain. This standardization also positions the U.S. more closely with international privacy frameworks, potentially easing cross-border data transfers and fostering greater global trust.
Conclusion: Embrace the Change for a Secure Future
The rollout of new federal data privacy guidelines in April 2026 marks a transformative period for businesses in the United States. While the journey to full compliance will require significant effort and investment, it presents a unique opportunity to strengthen data governance, bolster cybersecurity, and build deeper trust with customers. By adopting a proactive and strategic approach, organizations can not only meet their regulatory obligations but also position themselves for long-term success in an increasingly data-driven and privacy-conscious world.
Start your preparations today. Conduct that data audit, update those policies, train your staff, and invest in the right technologies. The future of your business in the digital economy depends on your commitment to protecting personal data. Embrace these changes, and turn regulatory challenges into a strategic advantage.





